GHCTF2025_PWN
Hello_world
签到题
开了pie,传后面的两位的字节就好
exp
1 | from pwn import * |
ret2libc1
这个看懂代码就好,直接ret2libc
exp
1 | from pwn import * |
ret2libc2
分析
这题有几个点需要特别注意
因为没有pop_rdi这个我们想要的gadget,但是前面存在一个格式化字符串漏洞,我们可以让函数地址跳转到前面漏洞的地址的位置
1 | ; __unwind { |
因为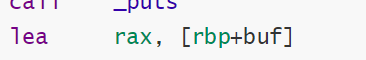
结合

我们在第一次函数返回的时候可以直接打印对我们输入的地址的进行格式化自字符串的利用(控制rax)
因为函数存在leave 指令,我们rbp的值不能随便覆盖,不然会出问题,我们只需保证rbp的地址有权限即可
所以我们选择bss段,注意后面执行其他指令可能会[rbp-0x7x],所以bss段要加上一个值
既然覆盖了rbp,那么我们还怎么知道溢出多少字节从而保证让函数执行到我们想要的位置呢
虽然后面的read会对rbp进行覆盖,但是通过调试可以知道,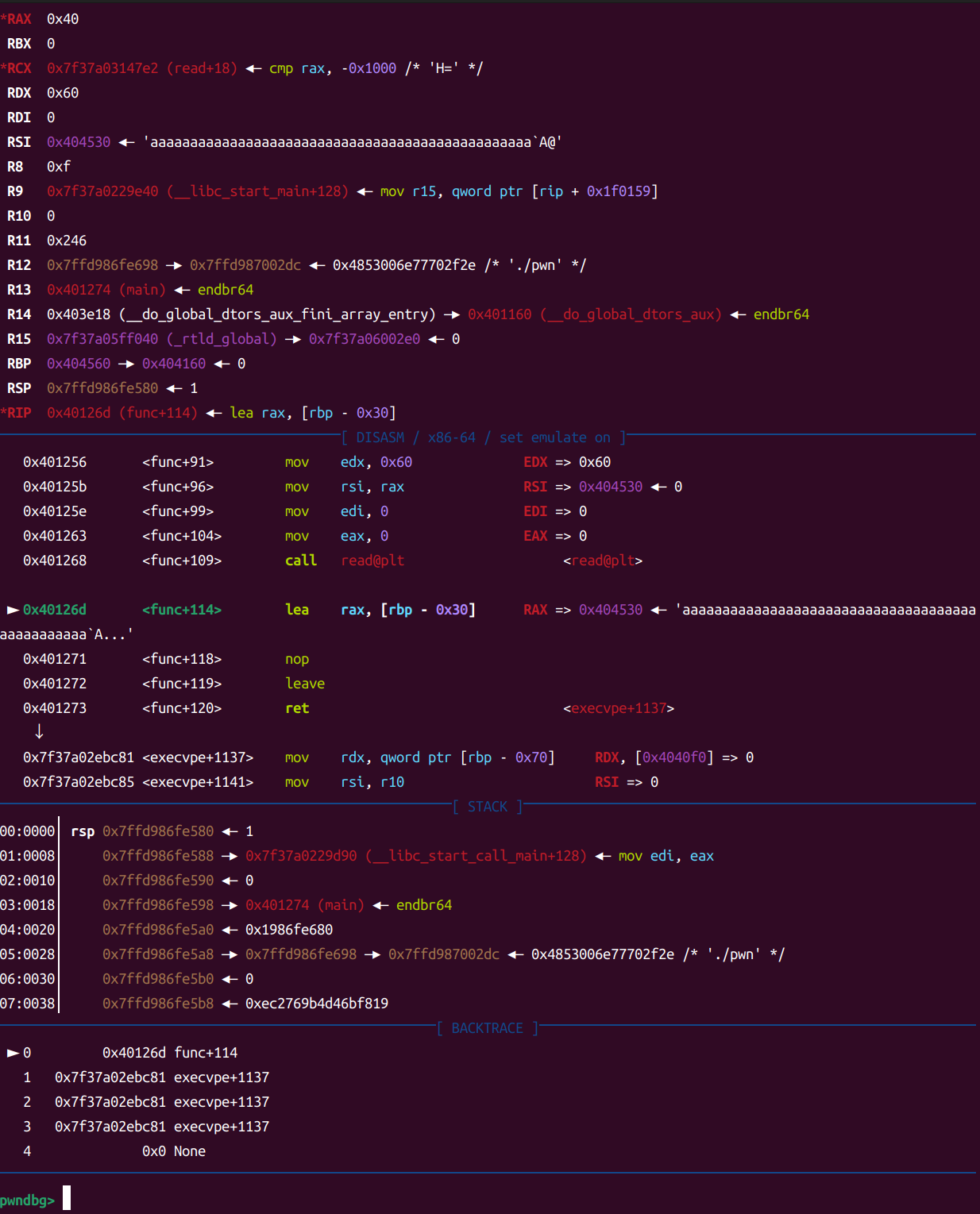
注意rbp的值,两次我传入的rbp覆盖的值不一样,加上先传入的rbp还是会先弹出,所以可以按照前面的长度进行覆盖
exp
1 | from pwn import * |
你真的会布置栈吗?
听说这个题目是国际赛题,好你个出题人,新生赛偷偷塞国际题目是吧
分析
题目给的很简单,就是打印一个图案中混着一个栈地址,并且有一个栈溢出,溢出后直接执行我们所需要的代码
1 | public _start |
但是这个题目考就考在gadgets的利用,我们来看看这个比赛给我们的gadgets
1 | print proc near ; CODE XREF: _start+F↓p |
因为全篇几乎没有一个ret,所以我们执行的gadget只能通过其他的方式来连接
注意,这里有很多的jmp r15 ,还有直接跳转到rsp地址或者rbx地址,所以我们可以通过这些寄存器实现函数的劫持,从而进行提权
我们知道要利用shellcode就需要执行execve(/bin/sh\x00,0,0)
也就是
1 | rdi---->/bin/sh\x00 |
因此我们可以直接利用这段代码实现寄存器的值的填入
1 | pop rsi |
这样子就可以控制我们想要的寄存器从而拿到shell
exp
1 | from pwn import * |
my_vm
分析
这题和buu上面的一题很像,VMpwn入门学习 | 鱼非愚具体可以看我这里的
仿照上面的操作我们,先对execute函数进行逆向
1 | 0x10: reg[high]=low |
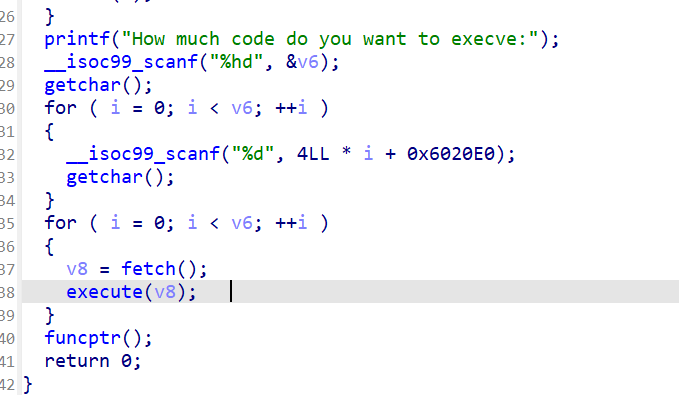
因为这题把后门函数给出来了,我们只需把funcptr这个函数的ptr地址改写为backdoor就行了
其实这题比较简单,大家可以先把上面我文章里面的复现完,再不看wp写这题,会清晰很多
exp
exp写的有点乱,主要是开始好几个点都看错了,后面直接缝缝补补了,没有大改
1 | from pwn import * |
持续更新中…
参考
本篇博客是复现博客,部分题目思路来自于网上,现在把参考的博客放在下面
[官方wp](https://iyheart.github.io/2025/03/09/CTFblog/write up系列blog/2025年/GHCTF2025-PWN方向wp/)

